What if the biggest threat to your enterprise security is not malware or ransomware but a trusted identity behaving suspiciously?
As enterprises accelerate digital transformation, identities have become the new security perimeter. Employees, customers, APIs, service accounts, and third-party integrations all rely on digital identities to access systems and data. This shift has made identity-based attacks one of the fastest-growing cybersecurity risks across industries such as banking, healthcare, SaaS, eCommerce, and large-scale enterprises.
An AI Identity Threat System helps organizations detect, analyze, and respond to abnormal identity behavior in real time. Unlike traditional security tools that rely on static rules, AI Identity Threat Software Development focuses on behavior-driven intelligence powered by machine learning and analytics. Enterprises today are actively exploring how to create an AI Identity Threat Software that can scale with complex infrastructures and evolving threats.
For CISOs, CTOs, security architects, and product leaders, developing an AI Identity Threat System is no longer experimental. It is becoming a strategic necessity. From insider threats to compromised credentials and machine identity misuse, the attack surface continues to grow.
Understanding the development process of AI Identity Threat Software helps decision-makers evaluate feasibility, cost, and long-term value. This blog is designed for enterprise leaders, cybersecurity teams, SaaS founders, and technology decision-makers who want a clear and practical view of building intelligent identity threat solutions that align with modern security demands.
AI Identity Threat Software is designed to spot risks that hide behind legitimate digital identities. Instead of looking only for known attack patterns, it focuses on how users, devices, and machine accounts behave once they are inside a system. This approach helps enterprises detect threats that traditional security tools often miss.
The software continuously analyzes identity data such as login activity, access requests, usage patterns, and privilege changes. Over time, it learns what normal behavior looks like for each identity and flags anything that feels out of place. This could be a sudden login from a new location, unusual access to sensitive data, or abnormal API usage.
For enterprises, AI Identity Threat Software acts as an intelligent layer over existing identity and access management systems, adding context, visibility, and faster response to identity-driven attacks without disrupting daily operations.
An AI Identity Threat System operates through a series of connected stages that help enterprises identify risky identity behavior early and respond effectively.
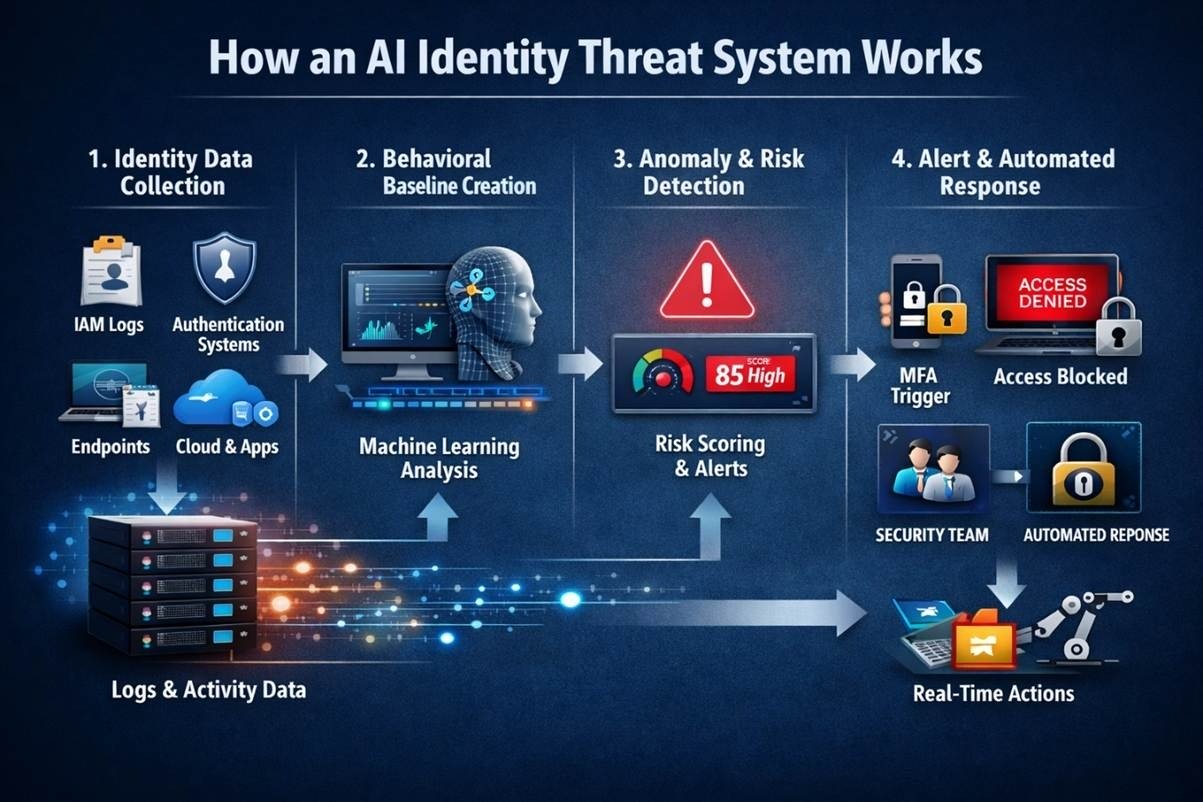
The system continuously gathers identity-related data from across the organization. This includes IAM logs, authentication events, endpoint activity, cloud access records, and application usage. Every interaction tied to a user or machine identity adds context to how that identity operates within the environment.
Using machine learning, the system studies this data to understand what normal behavior looks like for each identity. It learns patterns such as typical login times, access locations, devices used, and the type of resources accessed. These behavioral baselines are not fixed and evolve as roles, workloads, and access needs change.
When an identity behaves in an unexpected way, the system flags the activity as an anomaly. It then evaluates the level of risk by considering factors like behavior deviation, privilege level, and data sensitivity.
If the risk is high, the system generates alerts for security teams and can automatically take action. This may include enforcing multi-factor authentication, limiting access, or temporarily suspending the account to prevent further damage.
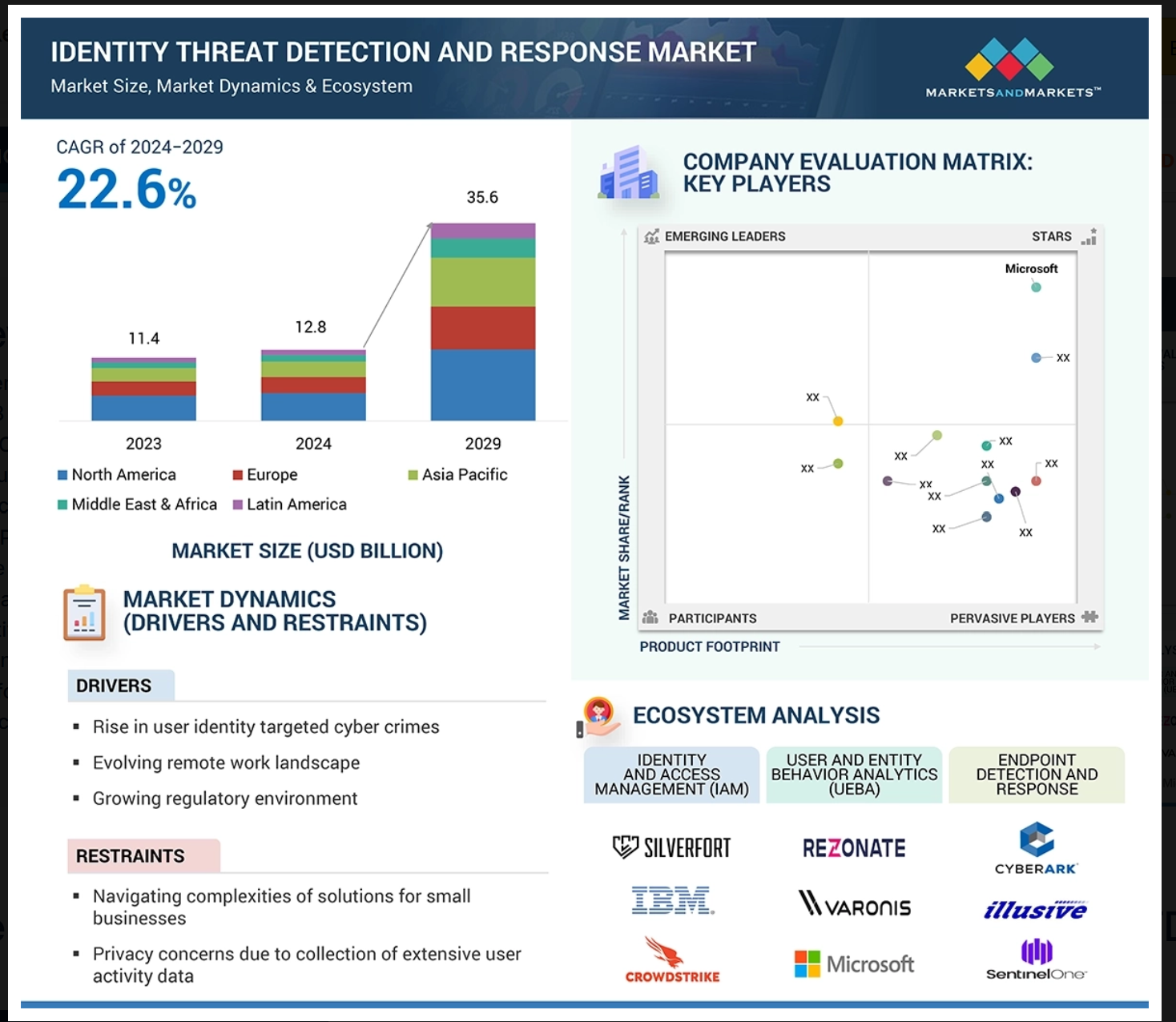
Identity-based attacks are no longer isolated security incidents. They are becoming a persistent business risk for enterprises operating in cloud-first and hybrid environments. According to MarketsandMarkets, the global Identity Threat Detection and Response market is expected to grow from USD 12.8 billion in 2024 to USD 35.6 billion by 2029, driven by the rise in identity-centric breaches and Zero Trust adoption.
Here’s some solid reason to invest in developing an AI Identity Threat Software:
For CISOs, this shift changes how security investments are evaluated. Firewalls and endpoint tools are no longer enough when attackers can enter systems using valid credentials. Investing in developing AI Identity Threat Software allows enterprises to monitor how identities behave after access is granted, which is where many advanced attacks unfold.
Building an AI Identity Threat System enables continuous behavioral analysis of users and machine identities. Rather than waiting for alerts after damage occurs, security teams gain early signals of misuse, privilege abuse, or compromised credentials. This proactive visibility significantly reduces breach dwell time and investigation effort.
The creation of AI Identity Threat Software for enterprises directly supports Zero Trust principles by treating every identity interaction as potentially risky. It also strengthens compliance by improving audit trails, access visibility, and incident documentation across regulated industries.
AI Identity Threat System development for enterprises offers CISOs greater control over security posture, data ownership, and customization. Instead of relying solely on third-party tools, organizations can build solutions aligned with their infrastructure, risk tolerance, and growth strategy.
For CISOs focused on resilience, scalability, and future readiness, investing in AI identity threat capabilities is no longer tactical. It is a strategic security decision.
Enterprises across industries are facing a sharp rise in identity-driven attacks that traditional security tools struggle to detect. AI Identity Threat Software Development enables organizations to gain deeper visibility into identity behavior and stop threats early. Below are some of the most impactful business use cases where building an AI Identity Threat System delivers real enterprise value.
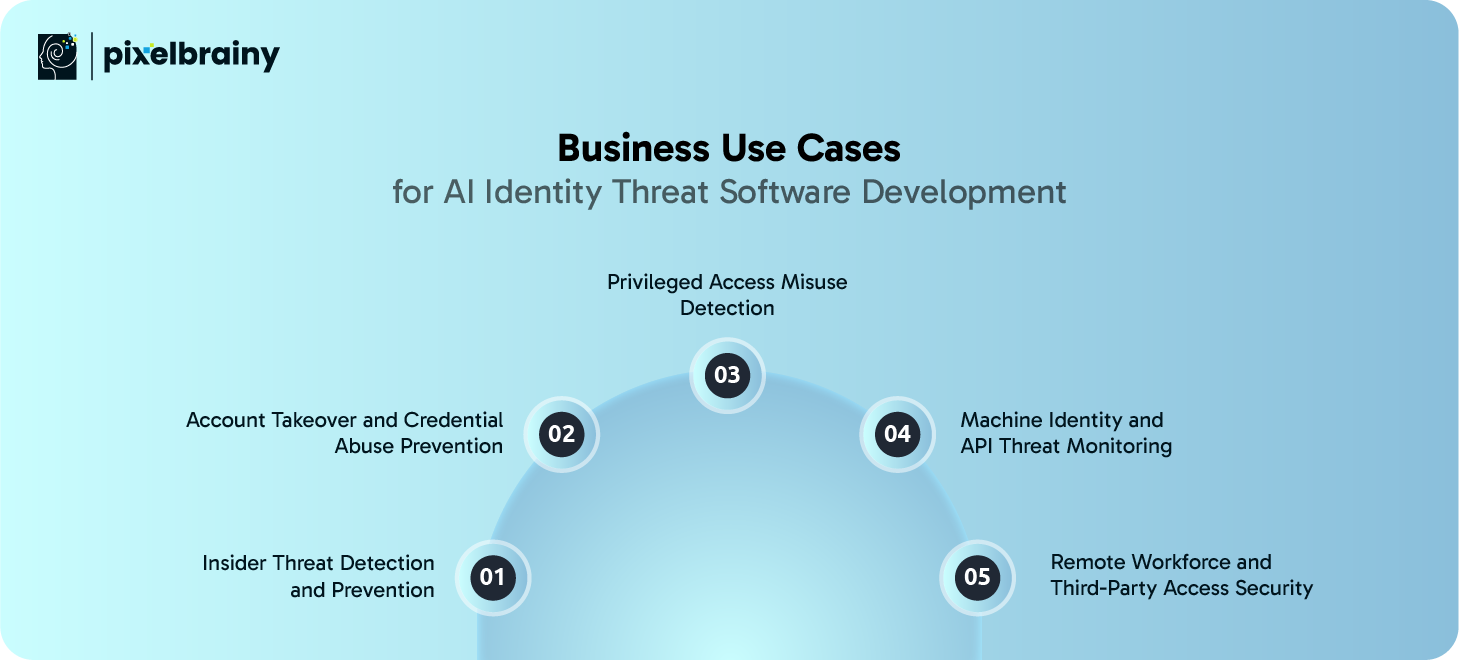
Insider threats remain one of the most difficult risks for enterprises to manage because the identities involved already have legitimate access. AI Identity Threat Software continuously monitors how employees, contractors, and partners interact with systems and data. Instead of relying on static rules, the system learns normal access patterns for each role and individual.
When an insider starts accessing sensitive resources outside their usual scope, working at unusual hours, or downloading data at abnormal volumes, the AI Identity Threat System flags these behaviors as potential risks. This helps security teams distinguish between normal work deviations and genuine malicious intent.
For large enterprises, this approach significantly reduces false alarms while improving early detection. By investing in developing AI Identity Threat Software, organizations gain the ability to prevent data leaks, intellectual property theft, and compliance violations without disrupting employee productivity.
Account takeover attacks continue to rise as attackers exploit stolen credentials from phishing, malware, and dark web marketplaces. AI Identity Threat System development for enterprises focuses on detecting subtle behavioral changes that indicate a compromised account rather than relying solely on failed login attempts.
The software analyzes login locations, device fingerprints, access velocity, and session behavior to identify inconsistencies. For example, a user logging in from a new geography and immediately accessing high-risk systems can be identified as suspicious even if credentials are valid.
By enabling real-time risk scoring and adaptive authentication, enterprises can automatically enforce additional verification or restrict access. The creation of AI Identity Threat Software for enterprises helps reduce fraud losses, protect customer trust, and strengthen identity security across digital channels.
Privileged accounts are prime targets for attackers because they provide extensive access across enterprise systems. AI Identity Threat Software Development helps monitor how administrators and service accounts use elevated privileges in day-to-day operations.
The system builds behavior baselines for privileged identities, including the commands executed, systems accessed, and timing of activities. When unusual privilege escalation, unauthorized configuration changes, or abnormal access patterns occur, alerts are triggered for immediate investigation.
For CISOs, building an AI Identity Threat System adds a critical layer of protection beyond traditional privileged access management tools. It reduces the risk of catastrophic breaches caused by compromised or misused privileged credentials while maintaining operational efficiency.
Modern enterprises rely heavily on machine identities such as APIs, service accounts, and automation scripts. These identities often have persistent access and limited oversight, making them attractive targets. AI Identity Threat Software monitors how machine identities interact with applications and infrastructure.
By learning normal request patterns, data access behavior, and usage frequency, the system can detect anomalies such as token misuse, unauthorized API calls, or abnormal data transfers. This is especially important in microservices and cloud-native environments.
Developing AI Identity Threat Software helps enterprises secure non-human identities that are often overlooked by traditional security tools. This use case is critical for preventing silent breaches and protecting cloud and application ecosystems.
Remote work and third-party integrations have expanded the enterprise identity perimeter. AI Identity Threat System development for enterprises allows organizations to monitor identity behavior across locations, devices, and networks without relying on static access rules.
The software evaluates risk based on context such as device posture, access timing, and resource sensitivity. Suspicious activity from remote users or external partners can be detected early and addressed through adaptive controls.
By investing in building an AI Identity Threat System, enterprises can safely support flexible work models while maintaining strong identity governance. This use case is especially valuable for industries with distributed teams and complex partner ecosystems.
These are the top business use cases where AI Identity Threat Software Development delivers measurable security, risk reduction, and operational value for modern enterprises.
AI identity threats do not originate from a single source, and enterprises rarely face just one type of risk. Employees, customers, administrators, APIs, and third-party users all introduce different identity challenges. Because of this, AI Identity Threat Detection Software is most effective when it is purpose-built around specific identity categories and business scenarios.
Below are the key types of solutions enterprises can develop, along with how they are used in real environments.
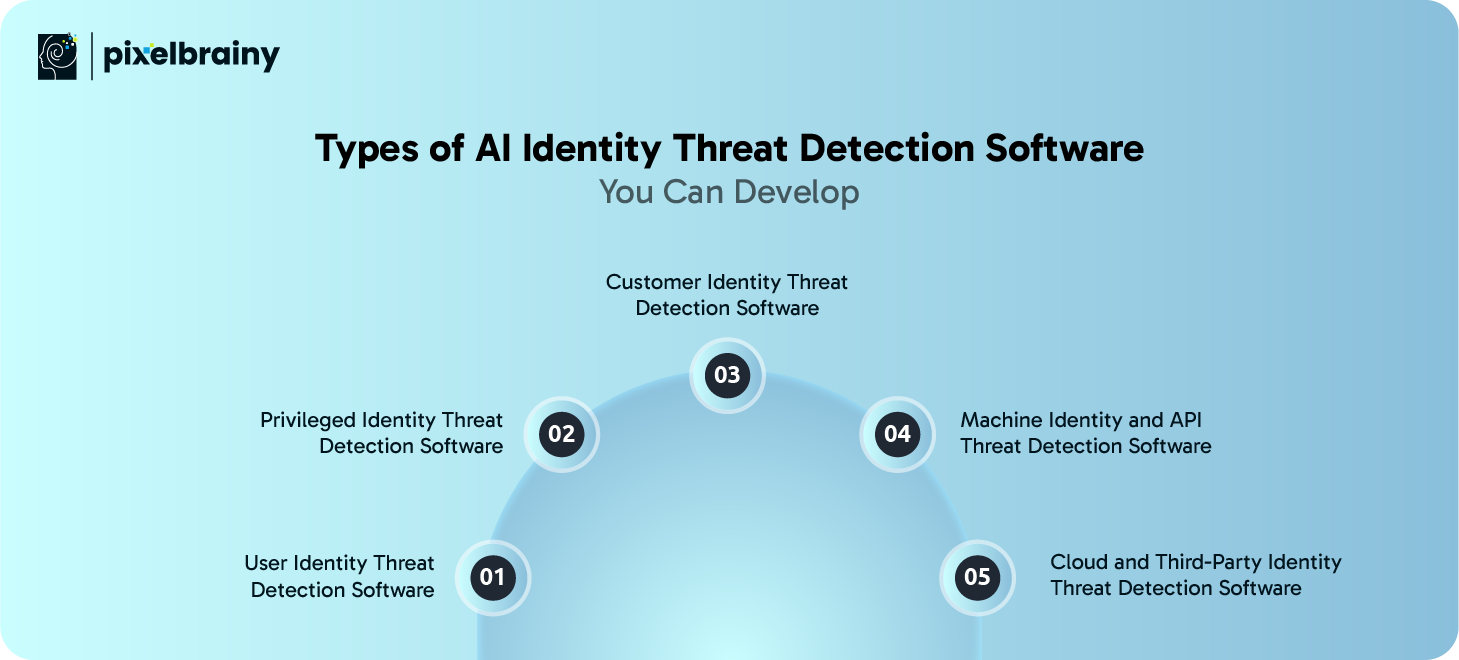
Designed to protect internal employees and workforce identities
This software focuses on understanding how employees normally access systems, applications, and data. It learns daily working patterns such as login times, device usage, locations, and access scope. Over time, it builds a trusted behavioral profile for each user.
When a user suddenly behaves differently, such as accessing sensitive systems outside their role or downloading unusual amounts of data, the system highlights this as a potential identity threat.
Common use cases:
This is often the first type of AI Identity Threat Software enterprises build because it delivers immediate visibility into workforce-related risks.
Focused on high-risk administrator and elevated accounts
Privileged identities have access to critical systems, making them extremely valuable targets for attackers. This software monitors how administrators and elevated service accounts use their privileges rather than just tracking access events.
It learns which systems are normally managed, what commands are typically executed, and when privileged actions usually occur. Any deviation from expected behavior is flagged for investigation.
Common use cases:
For enterprises managing complex infrastructure, building this type of AI Identity Threat System is essential for reducing high-impact breach risks.
Built to protect customer accounts and digital platforms
Customer-facing systems are frequent targets for fraud and account takeover attempts. This software analyzes how customers interact with applications by studying login behavior, navigation patterns, transaction flows, and session activity.
Instead of blocking users based on rigid rules, the system identifies subtle signals of abnormal behavior while allowing legitimate customers to continue their journey smoothly.
Common use cases:
This type of solution balances strong security with user experience, which is critical for customer-driven businesses.
Secures non-human identities operating behind the scenes
Modern enterprises rely heavily on APIs, service accounts, automation tools, and microservices. These machine identities often have persistent access and minimal human oversight.
This software monitors request patterns, access frequency, token usage, and data movement associated with machine identities. It detects misuse such as unauthorized API calls or abnormal data extraction.
Common use cases:
Developing this type of AI Identity Threat Software is critical as machine identities continue to outnumber human users.
Protects identities beyond the enterprise perimeter
As enterprises expand into cloud platforms and partner ecosystems, identity risk extends far outside internal networks. This software monitors access behavior across SaaS tools, cloud environments, vendors, and external collaborators.
It evaluates whether identities are accessing systems appropriately based on role, context, and business purpose.
Common use cases:
For enterprises with distributed ecosystems, this type of AI Identity Threat System ensures security without slowing down collaboration.
By developing the right combination of AI Identity Threat Detection Software types, enterprises can address identity risks across users, systems, and environments in a structured and scalable way. Choosing which type to build first depends on business priorities, threat exposure, and digital maturity.
Building an effective identity security platform requires more than basic monitoring. Enterprises investing in AI Identity Threat tool development need features that provide visibility, intelligence, and actionable response across identity lifecycles.
These core capabilities form the foundation of any reliable AI Identity Threat System designed for real-world enterprise environments.
| Feature | Description |
| Identity Behavior Monitoring | This feature continuously observes how users and machine identities interact with systems. It tracks login times, access frequency, and usage patterns across applications. Over time, it builds context around identity behavior that supports accurate threat detection. |
| Behavioral Baseline Modeling | The system learns what normal behavior looks like for each identity based on historical data. These baselines adapt as roles and responsibilities change. This allows the AI Identity Threat System to detect subtle deviations without excessive false alerts. |
| Anomaly Detection Engine | This component identifies behavior that deviates from established patterns. It focuses on abnormal access, unusual locations, and unexpected privilege use. Accurate anomaly detection is central to AI Identity Threat tool development. |
| Real-Time Risk Scoring | Each identity action is evaluated in real time and assigned a risk score. The score reflects factors such as behavior deviation and data sensitivity. This helps security teams prioritize responses efficiently. |
| Alerting and Notification System | When high-risk activity is detected, the system generates contextual alerts. These alerts include supporting data to reduce investigation time. Clear alerting improves response accuracy and speed. |
| Automated Response Controls | The software can automatically enforce security actions when risk thresholds are crossed. Actions may include access restriction or additional authentication. Automation reduces response delays during active threats. |
| IAM and SSO Integration | Seamless integration with identity and access management systems is essential. This ensures consistent identity visibility across platforms. Integration simplifies enterprise deployment and adoption. |
| Audit Logs and Activity Tracking | Detailed logs record identity actions and system responses. These logs support investigations and compliance reporting. Strong logging builds trust in the AI Identity Threat System. |
| Role and Privilege Context Awareness | The system understands what each identity is allowed to do based on role. It evaluates behavior against expected privilege boundaries. This prevents misuse of authorized access. |
| Machine Identity Visibility | Non-human identities such as APIs and service accounts are monitored continuously. Their behavior is analyzed like human users. This helps enterprises secure automated environments. |
| Cloud Identity Monitoring | The software tracks identity activity across cloud platforms and SaaS tools. It identifies risky access and misconfigurations. Cloud visibility is essential to build Identity Threat Software at scale. |
| Data Sensitivity Awareness | The system considers the sensitivity of accessed resources. Risk scoring increases when high-value data is involved. This helps prevent serious data exposure incidents. |
| Policy Configuration and Controls | Enterprises can define thresholds and response rules. Policies align detection with business requirements. Customization improves relevance and effectiveness. |
| Dashboards and Reporting | Visual dashboards provide a clear view of identity risks. Reports help stakeholders understand trends and incidents. Good reporting improves decision making. |
| Scalability and Performance Support | The platform must scale across large identity volumes. Performance remains consistent under high data loads. Scalability ensures long-term viability of the solution. |
These core features form the backbone of successful AI Identity Threat tool development. Together, they enable enterprises to build Identity Threat Software that delivers visibility, control, and confidence across identity ecosystems.
Once the foundation is in place, enterprises can strengthen security posture by adding advanced intelligence capabilities. These features enhance accuracy, automation, and adaptability for organizations aiming to develop Identity Threat Software Solutions that stay effective against evolving threats.
| Advanced Feature | Description |
| Predictive Identity Risk Modeling | This feature anticipates potential identity threats before they occur. It analyzes historical trends and behavioral signals. Predictive insights help security teams act early. |
| Adaptive Authentication Triggers | Authentication requirements change dynamically based on risk level. High-risk behavior can prompt stronger verification. This improves security without impacting normal users. |
| Explainable AI Insights | The system explains why an activity was flagged as risky. Transparency improves trust and usability. Explainable AI is critical in Identity Threat Software System development integrating AI. |
| Cross-Identity Correlation | Identity events across users, devices, and systems are correlated. This reveals coordinated or lateral movement attacks. Correlation improves detection accuracy. |
| Threat Intelligence Integration | External threat feeds enrich identity analysis. Known malicious indicators add context to behavior. Integration improves decision quality. |
| Continuous Learning Models | AI models adapt as identity behavior evolves. Learning occurs without manual reconfiguration. This keeps detection accurate over time. |
| Automated Incident Workflows | Identity incidents trigger predefined response workflows. Tasks are assigned automatically. This reduces manual effort during investigations. |
| Zero Trust Policy Enforcement | Every identity interaction is verified continuously. Trust is never assumed. This feature aligns with modern security frameworks. |
| Insider Risk Scoring | The system evaluates long-term risk associated with identities. Behavioral patterns contribute to risk profiles. This supports proactive insider threat management. |
| Multi-Environment Visibility | Identity activity is monitored across on-premise, cloud, and hybrid systems. Unified visibility simplifies security management. It is essential to develop Identity Threat Software Solutions at enterprise scale. |
Advanced capabilities elevate AI Identity Threat Systems from detection tools to intelligent security platforms. These features help enterprises stay resilient as identity threats grow more complex and persistent.
Building enterprise-grade identity security software requires a structured and thoughtful approach. The AI Identity Threat Software Development Process involves aligning security goals, business needs, and advanced AI capabilities into a scalable solution.
Below is a step-by-step breakdown that explains what is the process to make an AI Identity Threat Software for Enterprises, from concept to deployment.

Aim of this step: To clearly understand what identity threats the software must address and why the enterprise needs it.
Every successful Identity Threat System development with AI starts with clarity. Enterprises must identify their most critical identity risks, such as insider threats, account takeover, privileged misuse, or API abuse. This step involves close collaboration between CISOs, security teams, and business stakeholders to define goals, compliance requirements, and success metrics.
By documenting real-world scenarios and prioritizing use cases, teams can avoid building unnecessary features. This clarity ensures that efforts to build AI Identity Threat Software remain focused on measurable outcomes rather than generic security functions. A well-defined scope also helps Top AI development Companies estimate effort accurately and recommend the right architecture early in the process.
Aim of this step: To ensure the system has access to the right data sources for accurate identity analysis.
AI-based identity threat detection depends heavily on high-quality identity data. Enterprises must map all relevant sources including IAM systems, SSO platforms, cloud services, endpoints, applications, and APIs. This step defines how identity events will be collected, normalized, and stored securely.
Clear data pipelines reduce noise and improve AI model accuracy. During this phase, enterprises also define data privacy boundaries and compliance controls. A strong data foundation is essential when developing an AI Identity Threat Software System for Enterprises because weak or incomplete data leads to unreliable threat detection outcomes.
Aim of this step: To create a scalable and secure technical foundation for long-term growth.
System architecture defines how different components interact within the AI Identity Threat Software. This includes data ingestion layers, AI engines, alerting mechanisms, dashboards, and integrations with existing security tools. Architects must consider scalability, performance, and deployment environments such as cloud, hybrid, or on-premise.
At this stage, top AI product development companies often provide architecture blueprints that balance performance with security. Decisions made here impact system flexibility and future enhancements. A well-planned architecture ensures the AI Identity Threat Software Development Process remains adaptable as enterprise needs evolve.
Aim of this step: To validate the technical feasibility and effectiveness of AI models early.
Proof of Concept development is a critical step before full-scale investment. During PoC development, AI models are trained on limited datasets to test their ability to detect abnormal identity behavior. The goal is to confirm that AI techniques can deliver meaningful insights for defined use cases.
This phase helps enterprises refine algorithms, validate data assumptions, and identify potential limitations. PoC development reduces risk by proving value early. It also builds confidence among stakeholders that the AI Identity Threat Software System can deliver actionable security intelligence.
Aim of this step: To ensure the software is usable, intuitive, and operationally efficient.
Security tools often fail due to poor usability. Partnering with an experienced UI UX design company ensures that dashboards, alerts, and workflows are easy to understand and act upon. This step focuses on designing interfaces that reduce investigation time and cognitive load.
User journeys are mapped for security analysts, administrators, and executives. Visual clarity, contextual alerts, and simple navigation make the system effective in real-world environments. Strong UI and UX design plays a major role in successful AI Identity Threat Software adoption across enterprises.
Aim of this step: To build a functional version of the product with essential capabilities.
Minimum viable product development focuses on implementing core features such as behavior monitoring, anomaly detection, risk scoring, and alerting. The MVP allows enterprises to test the solution in live environments with limited scope.
Feedback collected during MVP development helps refine features, improve performance, and adjust detection logic. This step ensures the system delivers real value while remaining flexible. MVP development is a practical milestone in the journey to build AI Identity Threat Software that meets enterprise expectations.
Also Read: Top 10 AI MVP Development Companies in USA
Aim of this step: To ensure seamless operation within existing enterprise ecosystems.
The AI Identity Threat Software must integrate smoothly with IAM platforms, SIEM tools, ticketing systems, and cloud services. This step validates interoperability and ensures alerts and responses align with enterprise workflows.
Security validation testing is also performed to ensure data protection, access control, and compliance requirements are met. AI Integration testing ensures the software functions as part of a broader security architecture rather than an isolated tool.
Aim of this step: To maintain accuracy, performance, and relevance over time.
Once deployed, the system must be continuously monitored to ensure AI models remain effective. Identity behavior evolves, and AI models must adapt accordingly. Continuous learning, performance monitoring, and regular updates are essential.
Enterprises often work with Top AI development Companies for long-term support and optimization. This step ensures the AI Identity Threat Software continues to protect identities effectively as the organization grows and threat landscapes change.
Developing an AI Identity Threat Software System for Enterprises is a structured journey that combines strategy, design, AI intelligence, and operational readiness. When executed correctly, this process enables enterprises to build resilient identity security platforms that evolve with modern threats.
Understanding the financial scope is a critical step before starting any identity security initiative. When enterprises ask, how much will it cost to build AI Identity Threat Software, the answer depends on system depth, AI maturity, and enterprise scale.
On average, the AI Identity Threat Software Development Cost ranges between $30,000 to $250,000+, based on features, integrations, and long-term goals.
| Software Type | Estimated Cost | Development Timeline | What You Will Get |
| Basic AI Identity Threat Software (MVP) | $30,000 to $60,000 | 8 to 12 weeks | Core identity behavior monitoring, basic anomaly detection, limited dashboards, IAM integration, PoC validated models |
| Advanced AI Identity Threat Software | $70,000 to $150,000 | 4 to 6 months | Real-time risk scoring, automated alerts, adaptive authentication, cloud identity monitoring, improved UI UX design |
| Enterprise AI Identity Threat Software | $180,000 to $250,000+ | 6 to 9 months | End-to-end identity coverage, advanced AI models, machine identity monitoring, enterprise integrations, compliance reporting, scalable architecture |
The sophistication of AI models directly impacts the cost of developing an AI Identity Threat System. Basic statistical models are less expensive, while behavioral modeling and predictive analytics require more training, tuning, and compute resources. Advanced models can increase development budgets by $15,000 to $40,000, especially when custom algorithms are involved.
The number of identity data sources significantly affects development cost. Integrating multiple IAM systems, cloud platforms, and applications requires additional engineering effort. Expanding data ingestion pipelines can add $10,000 to $30,000 to the development budget of AI Identity Threat Software.
Working with a professional UI UX design company increases upfront costs but improves usability and adoption. Well-designed dashboards and workflows typically add $8,000 to $20,000, depending on complexity. This investment often reduces training and operational costs later.
Cloud-native deployments are generally more cost-effective than hybrid or on-premise setups. Infrastructure planning and scalability requirements can increase costs by $12,000 to $35,000, especially for enterprise-grade systems.
Enterprises in regulated industries need advanced audit logs, encryption, and compliance controls. These requirements can add $10,000 to $25,000 to the cost to create an AI Identity Threat Software Solutions that meet regulatory standards.
| Optimization Strategy | How It Helps | Estimated Cost Savings |
| Start With MVP Development | Focuses only on core features and validates value early | Save $30,000 to $70,000 |
| Reuse Existing IAM and Security Tools | Reduces integration and redevelopment effort | Save $15,000 to $40,000 |
| Phased Feature Rollout | Spreads development budget across stages | Save $20,000 to $50,000 |
| Cloud-Based Infrastructure | Lowers setup and maintenance costs | Save $10,000 to $25,000 |
| Partner With Experienced AI Teams | Avoids rework and design mistakes | Save $25,000+ |
Careful planning of scope and architecture allows enterprises to control the AI Identity Threat Software Development Cost while building a solution that scales with security and business needs.

Also Read: AI Software Development Cost: A Complete Software Cost Guide
Building a reliable and scalable AI Identity Threat System requires the right combination of AI frameworks, data infrastructure, security technologies, and frontend tools. The technology stack must support real-time identity monitoring, intelligent analysis, and seamless integration with enterprise environments.
Below is a practical overview of the core tools and technologies commonly used while developing an AI Identity Threat Software System.
| Technology Layer | Tools and Technologies | Purpose and Role |
| Programming Languages | Python, Java, Scala | Python is widely used for AI model development and data processing. Java and Scala support backend services and large-scale data pipelines. These languages form the foundation of Identity Threat System development with AI. |
| AI and Machine Learning Frameworks | TensorFlow, PyTorch, Scikit-learn | These frameworks are used to build, train, and deploy behavioral analysis and anomaly detection models. They enable pattern learning and continuous improvement of threat detection accuracy. |
| Data Processing and Analytics | Apache Spark, Kafka, Flink | These tools handle large volumes of identity data in real time. They support streaming, aggregation, and normalization of logs from multiple identity sources. |
| Database and Storage | PostgreSQL, MongoDB, Elasticsearch | Structured and unstructured data storage is essential for identity logs and behavioral history. Elasticsearch enables fast search and analytics across identity events. |
| IAM and Security Integrations | Okta, Azure AD, Auth0 APIs | Integration with identity providers allows real-time access to authentication and authorization events. This ensures accurate identity visibility across systems. |
| Cloud Platforms | AWS, Azure, Google Cloud | Cloud platforms provide scalability, compute power, and secure infrastructure. They support flexible deployment models for enterprise identity threat solutions. |
| API and Backend Frameworks | Node.js, Spring Boot, FastAPI | Backend frameworks handle data ingestion, processing, and communication between system components. They enable smooth integration with enterprise tools. |
| UI and Frontend Technologies | React, Angular, Vue.js | These technologies are used to build dashboards and visualization interfaces. A clear UI improves usability for security teams and decision-makers. |
| Security and Compliance Tools | Encryption libraries, IAM policies, audit frameworks | These tools protect sensitive identity data and ensure compliance with regulations. Security controls are essential for enterprise adoption. |
| Monitoring and DevOps | Docker, Kubernetes, Prometheus | Containerization and monitoring tools ensure performance, reliability, and scalability. They support continuous deployment and system stability. |
Choosing the right AI tools and technology stack ensures that an AI Identity Threat System is secure, scalable, and capable of delivering real-time identity intelligence for enterprise environments.
As identity-based attacks continue to dominate modern breach scenarios, several AI-powered platforms have emerged as clear leaders in identity threat detection and response. These solutions stand out because of their ability to analyze identity behavior at scale, reduce detection time, and integrate seamlessly into enterprise security ecosystems.
Below is a restructured and more readable overview of the top AI Identity Threat Software solutions shaping the market today.
Best suited for enterprises using Microsoft ecosystems
Microsoft Entra combined with Defender for Identity provides deep visibility into identity risks across cloud and on-premise environments. The platform analyzes authentication traffic, credential usage, and directory activity to detect threats such as credential theft, lateral movement, and privilege escalation.
What makes this solution powerful is its native integration with Azure Active Directory, Microsoft 365, and the broader Microsoft security stack. Security teams benefit from unified dashboards, automated risk signals, and response workflows that reduce manual effort. For enterprises already operating within Microsoft environments, this platform delivers strong identity protection without the need for complex integrations.
Ideal for organizations seeking unified threat visibility
CrowdStrike Falcon extends its well-known endpoint protection capabilities into identity threat detection. The platform correlates identity signals with endpoint and workload telemetry to identify compromised credentials and abnormal access behavior.
By combining identity data with real-time threat intelligence, Falcon provides security teams with contextual insights rather than isolated alerts. This holistic approach helps enterprises detect identity-based attacks that are part of broader intrusion campaigns. Its cloud-native design also makes it highly scalable for large, distributed environments.
Focused on behavioral analysis and signal clarity
Vectra AI specializes in using machine learning to detect identity attacks that bypass traditional controls. Its platform continuously analyzes identity behavior across hybrid and cloud infrastructures to identify suspicious access patterns and lateral movement.
Vectra AI is known for reducing alert fatigue by prioritizing high-risk identity threats. This allows security teams to focus on the most critical incidents first. It is particularly effective for enterprises managing complex environments where identity signals are spread across legacy and modern systems.
Strong fit for identity governance and risk-driven access
Saviynt offers AI-driven identity threat detection as part of a broader identity governance framework. The platform monitors identity access, entitlements, and behavior to detect anomalies and enforce least-privilege principles.
Saviynt stands out for enterprises that want to combine identity governance, compliance, and threat detection into a single platform. Its AI capabilities help automate access decisions, identify risky permissions, and support remediation workflows. This makes it particularly valuable in regulated industries with strict compliance requirements.
Designed for modern cloud and machine identity environments
Permiso focuses on unifying visibility across human, machine, and cloud identities. Its identity graph maps relationships between identities, permissions, and resources to identify hidden risks and suspicious behavior.
Permiso is well-suited for enterprises operating in multi-cloud and DevOps-heavy environments. By providing real-time risk context and prioritization, it helps security teams detect and respond to identity threats that traditional tools often overlook. Its approach aligns well with modern Zero Trust and cloud-native security strategies.
| Platform | Core Strength | Identity Coverage | Best Fit For |
| Microsoft Entra + Defender for Identity | Deep Microsoft ecosystem integration | Workforce and privileged identities | Microsoft-centric enterprises |
| CrowdStrike Falcon Identity Protection | Unified endpoint and identity visibility | Workforce and endpoint-linked identities | Large distributed enterprises |
| Vectra AI | Behavioral analysis with strong signal prioritization | Workforce and hybrid identities | SOC-driven security teams |
| Saviynt | Identity governance with AI risk detection | Workforce, privileged, and access entitlements | Regulated industries |
| Permiso | Unified human and machine identity visibility | Cloud, machine, and API identities | Cloud-native enterprises |
These platforms represent the current leaders in AI-driven identity threat detection, each addressing different enterprise needs. Choosing the right solution depends on factors such as existing infrastructure, cloud adoption level, and the complexity of identity environments.
Choosing the right business model is just as important as building the technology itself. The way AI Identity Threat Software is packaged, priced, and delivered directly impacts adoption, scalability, and long-term revenue.
Below are the most effective business models enterprises and product companies consider when launching identity threat solutions.
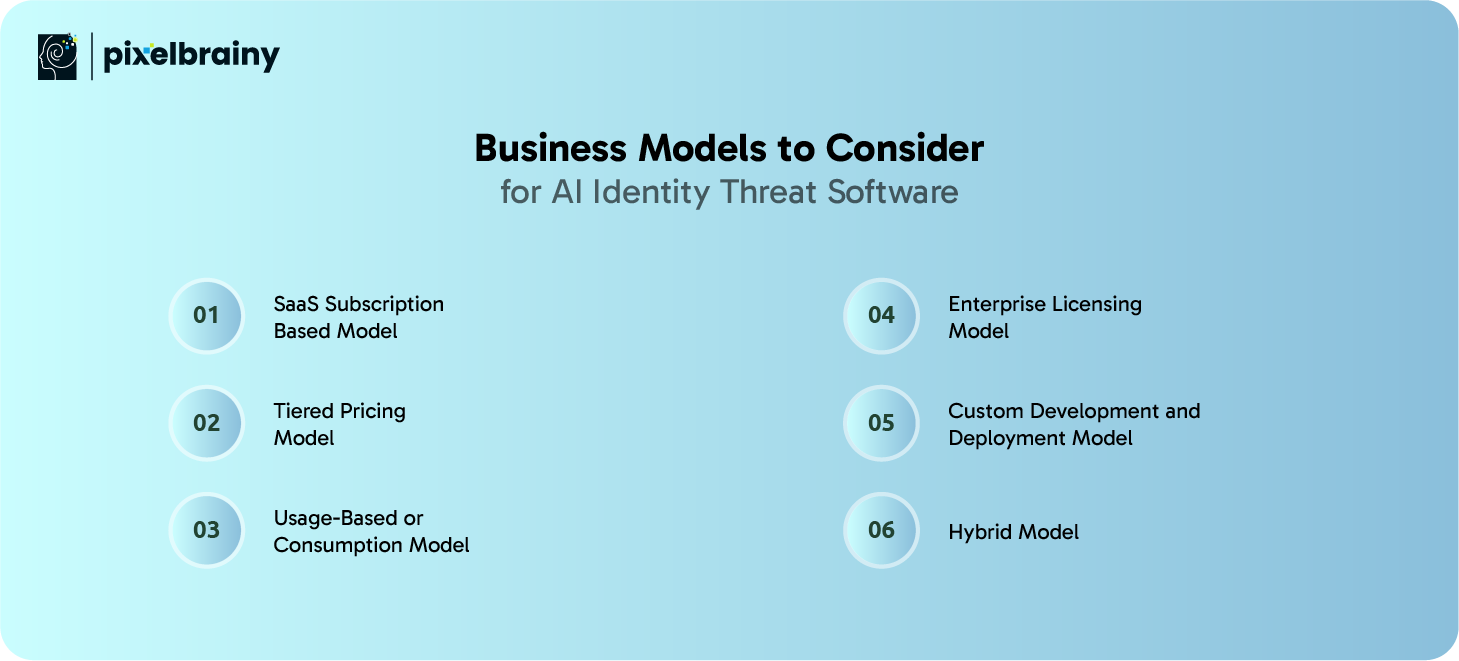
This is the most common and scalable business model for AI Identity Threat Software. The solution is delivered as a cloud-based service with recurring monthly or annual subscriptions.
Why this model works:
This model is ideal for enterprises looking for rapid deployment and lower upfront investment.
In this approach, the software is offered in multiple tiers such as basic, advanced, and enterprise, each with different feature sets.
Key advantages:
Tiered pricing aligns well with AI Identity Threat Software that evolves over time.
Pricing is based on usage metrics such as number of identities monitored, events processed, or data volume analyzed.
Best suited for:
This model provides flexibility while encouraging efficient system usage.
Under this model, organizations pay a fixed annual or multi-year license fee for unlimited or predefined usage.
Why enterprises prefer it:
This model works well for large enterprises with stable identity environments.
Some organizations prefer fully customized AI Identity Threat Software built specifically for their infrastructure and security policies.
Common use cases:
This model offers maximum control but typically involves higher upfront investment.
A hybrid model combines SaaS delivery with optional customization, on-premise components, or premium services.
Why it is gaining popularity:
Hybrid models appeal to enterprises transitioning between legacy and modern systems.
Selecting the right business model ensures AI Identity Threat Software not only meets security needs but also supports sustainable growth and long-term adoption.
Building an enterprise-grade identity security platform requires more than just technical skills. It demands deep understanding of identity risks, AI capabilities, enterprise workflows, and long-term scalability. As an experienced AI development company, PixelBrainy supports enterprises at every stage of the journey, from strategy to deployment, helping them confidently answer how to make an AI Identity Threat Software that delivers real security outcomes.
PixelBrainy offers complete AI Identity Threat Software Development Solutions tailored to enterprise needs. The process begins with understanding your identity landscape, threat exposure, and compliance requirements. Our teams design systems that align with your existing IAM, cloud platforms, and security tools, ensuring smooth adoption and minimal disruption.
From architecture design to AI model development, PixelBrainy focuses on building systems that analyze identity behavior accurately and scale with business growth. Whether the goal is workforce identity protection, privileged access monitoring, or machine identity security, we deliver solutions designed for real-world enterprise environments.
PixelBrainy specializes in the development of AI Identity Threat System using advanced behavioral analytics, anomaly detection, and risk scoring models. Our engineers and data scientists work closely to ensure that AI models remain explainable, adaptable, and effective over time. We emphasize continuous learning so that identity threat detection evolves alongside user behavior and organizational changes.
Strong UI and UX design is also a priority. Security teams need clear insights, not complex dashboards. PixelBrainy designs intuitive interfaces that help analysts quickly understand risks and take action without unnecessary complexity.
In one recent engagement, PixelBrainy partnered with a large enterprise operating in a hybrid cloud environment with thousands of workforce and machine identities. The organization faced challenges detecting credential misuse and abnormal access behavior across distributed systems.
PixelBrainy led the end-to-end development of an AI Identity Threat System, starting with PoC development to validate AI models on identity logs. We then delivered an MVP focused on behavior monitoring, anomaly detection, and real-time risk scoring. The solution was integrated with existing IAM and SIEM tools, enabling seamless security operations.
Within months of deployment, the enterprise achieved earlier detection of identity misuse, reduced false alerts, and improved investigation efficiency. The project remains confidential, but it stands as a strong example of how tailored AI-driven identity security can deliver measurable value.
As a trusted AI development company, PixelBrainy combines strategic guidance, technical expertise, and long-term support. We help enterprises move from concept to production with confidence, ensuring that their AI Identity Threat Software is secure, scalable, and future-ready.
If your organization is exploring how to make an AI Identity Threat Software or modernize identity security, PixelBrainy can be your development partner throughout the journey.
Identity has become the new security perimeter for modern enterprises, and protecting it requires more than traditional tools and static rules. AI-driven identity threat solutions enable organizations to detect subtle misuse, respond faster to incidents, and reduce risk across workforce, customer, and machine identities. From defining use cases and selecting the right technology stack to managing costs and choosing the right business model, successful AI Identity Threat Software Development demands a clear strategy and experienced execution.
Enterprises that invest early in intelligent identity protection gain stronger security posture, improved compliance, and long-term resilience against evolving threats. With the right development approach and trusted partner, organizations can transform identity security into a proactive defense capability rather than a reactive control.
Ready to secure your enterprise identities with AI? Book an appointment today to discuss your AI Identity Threat Software roadmap.
Yes, most enterprise-grade AI Identity Threat Software is designed to complement existing IAM, SIEM, and SOC tools rather than replace them. It adds an intelligence layer that analyzes identity behavior across systems and feeds risk insights back into your current security workflows, improving visibility without disrupting operations.
Enterprises often begin seeing measurable value within a few weeks of deployment. Early benefits include reduced false alerts, clearer visibility into risky identity behavior, and faster investigations. As AI models learn over time, detection accuracy and operational efficiency continue to improve.
When designed correctly, it does the opposite. By focusing on behavioral risk instead of static rules, the software applies additional security only when risk is detected. This helps maintain smooth user experiences while still protecting sensitive systems and data.
Organizations with large user bases, remote workforces, cloud infrastructure, or heavy API usage benefit the most. Industries such as finance, healthcare, SaaS, and eCommerce see strong returns due to their high exposure to identity-based threats.
Data privacy is managed through encryption, access controls, and strict data governance policies. AI models focus on behavioral patterns rather than personal content, and enterprise deployments can be configured to meet regional and industry-specific compliance requirements.
The right choice depends on your enterprise needs. Off-the-shelf tools offer faster deployment, while custom-built solutions provide greater control, customization, and alignment with internal systems. Many enterprises start with existing tools and later invest in custom development as identity complexity grows.
About The Author
Sagar Bhatnagar
Sagar Sahay Bhatnagar brings over a decade of IT industry experience to his role as Marketing Head at PixelBrainy. He's known for his knack in devising creative marketing strategies that boost brand visibility and market influence. Sagar's strategic thinking, coupled with his innovative vision and focus on results, sets him apart. His track record of successful campaigns proves his ability to utilize digital platforms effectively for impactful marketing efforts. With a genuine passion for both technology and marketing, Sagar continuously pushes PixelBrainy's marketing initiatives to greater success.


Transform your ideas into reality with us.
Working with the PixelBrainy team has been a highly positive experience. They understand the design requirements and create beautiful UX elements to meet the application needs. The dev team did an excellent job bringing my vision to life. We discussed usability and flow. Sagar worked with his team to design the database and begin coding. Working with Sagar was easy. He has the knowledge to create robust apps, including multi-language support, Google and Apple ID login options, Ad-enabled integrations, Stripe payment processing, and a Web Admin site for maintaining support data. I'm extremely satisfied with the services provided, the quality of the final product, and the professionalism of the entire process. I highly recommend them for Android and iOS Mobile Application Design and Development.

Great experience working with them. Had a lot of feedback and I found that unlike most contractors they were bugging me for updates instead of the other way around. They were extremely time conscience and great at communicating! All work was done extremely high quality and if not on time, early! They were always proactive when it comes to communication and the work is great/above par always. Very flexible and a great team to work with! Goes above and beyond to present us with multiple options and always provides quality. Amazing work per usual with Chitra. If you have UI/UX or branding design needs I recommend you go to them! Will likely work with them in the future as well, definitely recommended!

PixelBrainy is a joy to work with and is a great partner when thinking through branding, logo, and website layout. I appreciate that they spend time going into the "why" behind their decisions to help inform me and others about industry best practices and their expertise.

I hired them to design our software apps. Things I really like about them are excellent communication skills, they answer all project suggestions and collaborate right away, and their input on design and colors is amazing. This project was complex and needed patience and creativity. The team is amazing to do business with. I will be using them long-term. Glad to see there are some good people out there. I was afraid to try and outsource my project to someone but I am glad I met them! I really can't say enough. They went above and beyond on this project. I am very happy with everything they have done to make my business stand out from the competition.

It was great working with PixelBrainy and the team. They were very responsive and really owned the project. We'll definitely work with them again!

I recently worked with the PixelBrainy team on a project and I was blown away by their communication skills. They were prompt, clear, and articulate in all of our interactions. They listened and provided valuable feedback and suggestions to help make the project a success. They also kept me updated throughout the entire process, which made the experience stress-free and enjoyable.

PixelBrainy is very good at what it does. The team also presents themselves very professionally and takes care of their side of things very well. I could fully trust them taking up the design work in a timely and organised manner and their attention to detail saved us lots of effort and time. This particular project was quite intense and the team showed that they function very well under pressure. Very much looking forward to working with her again!

It's always an absolute pleasure working with them. They completed all of my requests quickly and followed every note I had for them to a T, which made our process go smoothly from start to finish. Everything was completed fast and following all of the guidelines. And I would recommend their services to anyone. If you need any design work done in the future, PixelBrainy should be your first call!

They took ownership of our requirements and designed and proposed multiple beautiful variants. The team is self-motivated, requires minimum supervision, committed to see-through designs with quality and delivering them on time. We would definitely love to work with PixelBrainy again when we have any requirements.

PixelBrainy was a big help with our SaaS application. We've been hard at work with a new UI/UX and they provided a lot of help with the designs. If you're looking for assistance with your website, software, or mobile application designs, PixelBrainy and the team is a great recommendation.

PixelBrainy designers are amazing. They are responsive, talented, and always willing to help craft the design until it matches your vision. I would recommend them and plan to continue them for my future projects and more!!!

They were awesome! Did a good job fast, and good communication. Will work with them again. Thank you

Creative, detail-oriented, and talented designers who take direction well and implement changes quickly and accurately. They consistently over-delivered for us.

PixelBrainy team is very talented and creative. Great designers and a pleasure to work with. PixelBrainy is an excellent communicator and I look forward to working with them again.

PixelBrainy has a very talented design team. Their work is excellent and they are very responsive. I enjoy working with them and hope to continue on all of our future projects.
